In an IoT, IIoT, or OT penetration test, the security of networked devices, industrial control systems, and embedded systems is comprehensively assessed. The objective is to identify vulnerabilities in hardware, firmware, and communications that could lead to the compromise of the device, the surrounding infrastructure, or the data being processed.
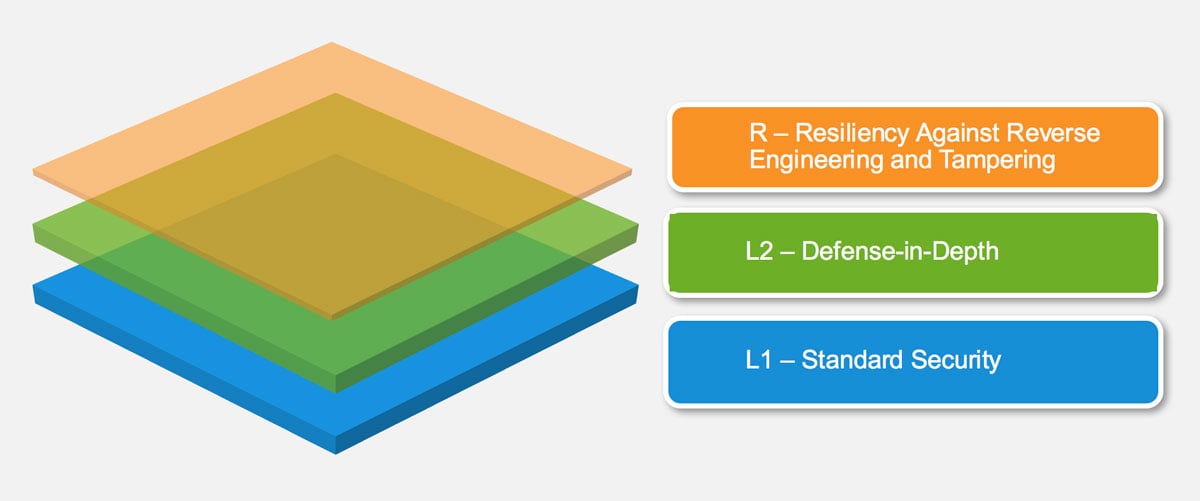
At the outset, the device’s hardware components are identified and analysed. This includes, among other things, processors, memory components, debug interfaces (e.g. JTAG, UART, SWD), as well as additional communication modules. Subsequently, it is examined whether existing security mechanisms such as secure boot, debug locks, memory protection, or physical safeguards can be bypassed. A successful bypass may, for example, allow the extraction or manipulation of firmware, sensitive configuration data, or cryptographic key material.
Depending on the device’s functionality and the available interfaces, further tests are performed. These include, but are not limited to:
- Manipulation and analysis via physical interfaces such as USB or touchscreens
- Network-based attacks over Ethernet, Wi‑Fi, or cellular networks
- Protocol-specific testing of industrial communication protocols such as Modbus, Profibus, Profinet, Ethernet/IP, CAN, CANopen, or OPC UA
- Verification of authentication, authorisation, and encryption mechanisms
- Analysis of update and maintenance processes (e.g. firmware updates, remote management)
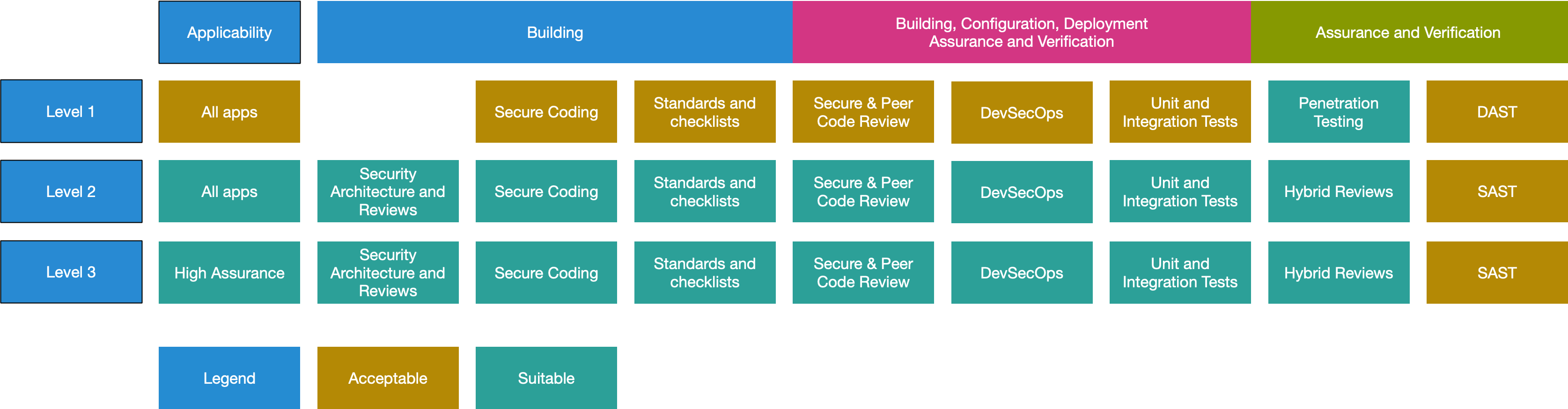
If required, the device firmware is additionally examined in accordance with the OWASP Firmware Security Testing Methodology. This includes both static analysis of the firmware image (e.g. file systems, configuration files, hardcoded secrets, known vulnerabilities in libraries) and dynamic analysis through emulation or runtime analysis of the firmware. This approach makes it possible to assess the actual behaviour of the system under attack conditions.
For a structured security assessment, the test is aligned with established best practices and standards, including:
- OWASP IoT Top 10 for identifying common vulnerabilities in IoT systems
- OWASP Firmware Security Testing Methodology for firmware analysis
- IEC 62443 as a reference framework for industrial automation and OT security