Team
Other Services
BASIC SECURITY HEALTH CHECK
The service for companies that want to take the first step into cyber security. Broad, automated and cost-saving.
AD SECURITY IMPROVEMENT
The IT core of your company (Active Directory) is checked for widespread misconfigurations. Ransomware, which often targets and exploits these vulnerabilities, is thus rendered ineffective.
SYSTEM AUDIT
Client or server audits to check systems for vulnerabilities and compliance with best practices.
Research and Insights
Plaintext in Memory: Revisiting Browser Password Security
Initial situation
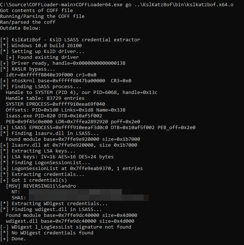
Experience Report: AI-Assisted BOF Development in Red Teaming
Over the past few days, I have been exploring how a current credential dumping tool like KslKatz can be efficiently ported into a Beacon Object File...
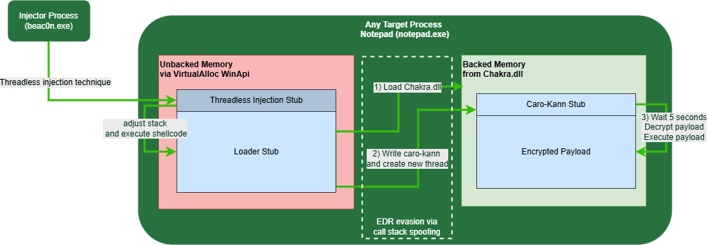
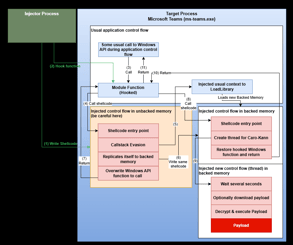
Threadless Ops II – Enhanced Evasion
The process injection technique via threadless injection that we discussed in our first blog post has seen more adoption in the meantime. For...
The Sins Of NTLMv1
In the past year, one particular configuration in our clients' Active Directory (AD) domains has repeatedly caught our attention - the usage of...
The next milestone for successful growth
Avantguard cyber security was transformed from a limited liability company (GmbH) into a stock corporation (AG) in November 2024. This was a major...













.jpg)